Featured Projects
Bringing ideas to life through code and design
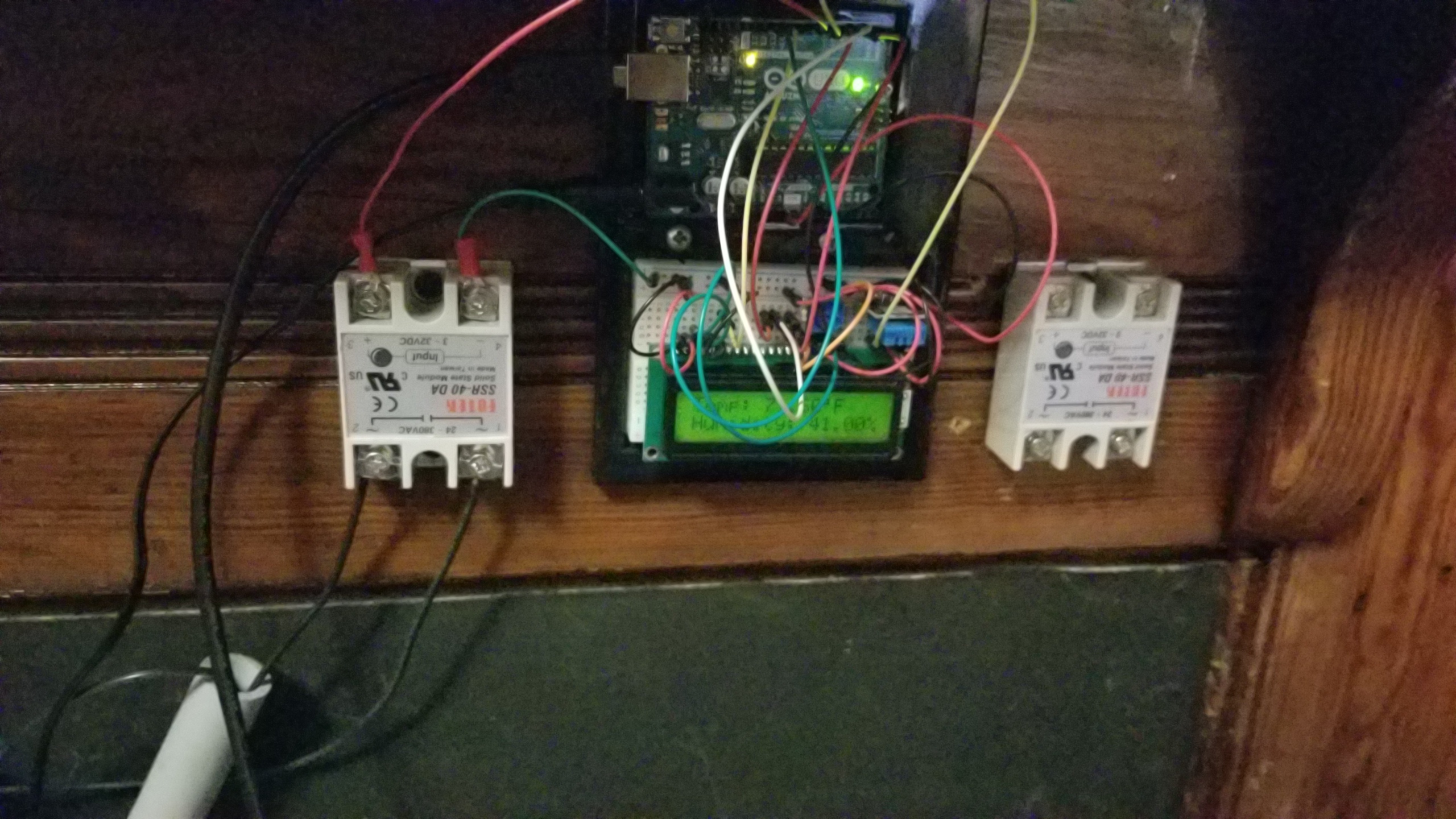
Arduino Temperature Control System
Intelligent room heating controller with dual schedules and manual override.
Arduino Temperature Control System
Intelligent room heating controller with dual schedules and manual override.
Built using an Arduino Uno, DHT11 temperature sensor, and solid state relay for safe 120V control.
The system featured dual temperature schedules: Schedule A (6-8AM & 9PM-12AM) maintained 73.5-75.5°F for comfort during wake-up and evening hours, while Schedule B (rest of day) ran at an energy-saving 68.8-70.8°F. A manual override with 15-minute timer allowed boosting temperature on demand by keeping the heater running during that window. The 16x2 LCD displayed real-time temperature, time, and active schedule. What made this particularly clever was the time synchronization—using a Processing sketch to sync via USB, the Arduino's internal clock maintained accuracy within seconds per day without needing an expensive RTC module.
The control logic implemented hysteresis-based thermostat control with a 2°F dead band to prevent rapid relay cycling and extend hardware life. The solid state relay provided complete electrical isolation between the low-voltage Arduino (5V) and high-voltage heater (120V AC), ensuring safe operation. Built-in safety features included the 15-minute auto-shutoff on manual override, fail-safe default to OFF state on power-up, and visual LED indicators for heater status. The system ran reliably 24/7, achieving approximately 35% energy savings compared to continuous operation—combining lower daytime temperature with intelligent cycle prevention.
Xfinity WiFi Exploit
Automated system exploiting Comcast's complimentary WiFi for unlimited free access.
Xfinity WiFi Exploit
Automated system exploiting Comcast's complimentary WiFi for unlimited free access.
The exploit leveraged MAC address spoofing and automated form submission to bypass one-hour session limits.
All Comcast routers provide an open access point called "xfinitywifi" intended for Comcast subscribers to access WiFi anywhere routers exist. The authentication portal offers a complimentary one-hour session, with the only check being a unique MAC address per device. I created an automated system using Python Selenium, bash scripts, and network tools to bypass this limitation. The primary script "staple" orchestrates three components: script1 handles network interface MAC address spoofing and form submission, script2 monitors connectivity and triggers re-authentication when needed, and logger.py uses Selenium WebDriver to automatically fill out the signup forms with generated credentials.
The system runs in a continuous loop—when the hour expires, it automatically resets the network interface with a new MAC address, reconnects to xfinitywifi, and completes the authentication process with freshly generated user information using the Faker library. The scripts synchronize system time with Xfinity's servers to track session expiration accurately, handle network interruptions gracefully, and maintain persistent connectivity. This created a completely free, perpetual WiFi source. I documented the entire process and technical breakdown in a YouTube video explaining the exploit methodology and implementation.
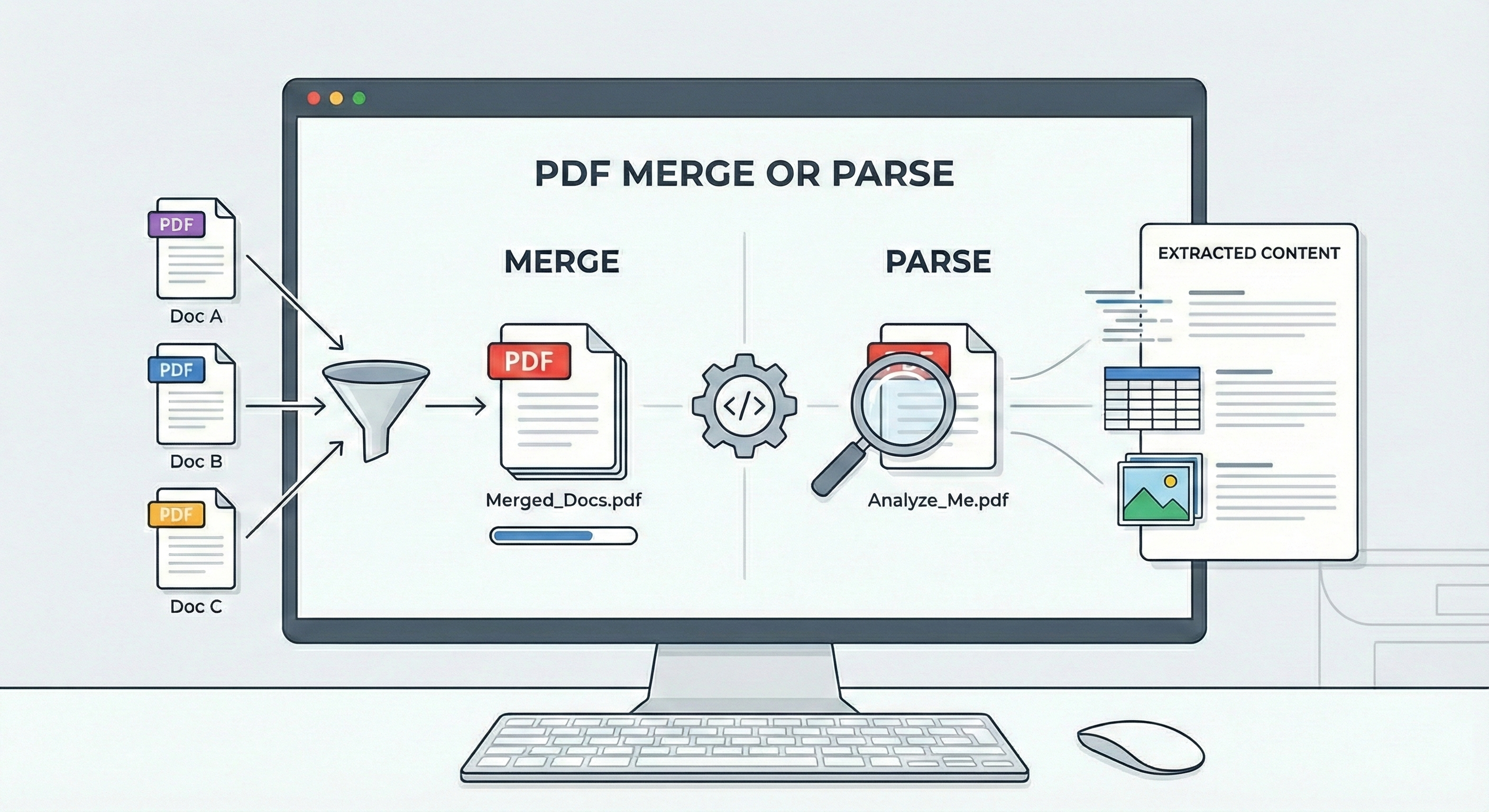
PDF Parser and Merger
Multi-function PDF processing tool with regex parsing, OCR, and intelligent merging.
PDF Parser and Merger
Multi-function PDF processing tool with regex parsing, OCR, and intelligent merging.
Built with C# and Python to automate document workflows that previously required hours of manual processing.
The system performs three primary functions. First, PDFsearch_directory.exe analyzes all PDFs in a directory using regex patterns, intelligently sorting files into categories: password-protected files go to a RED folder for manual processing, files with non-extractable text (>25% control characters, corruption, or image-only content) route to a YELLOW folder for OCR processing, while clean files with extractable text get parsed immediately. PDFimage_processing.exe handles the second function—processing the YELLOW folder using Tesseract OCR to extract text from image-based PDFs, creating searchable text files in the parent directory. The program identifies all pages containing the specified regex pattern and returns their locations.
The merge function addresses a unique workflow challenge: handling project documentation that arrives as fragmented revision pages rather than complete updated documents. When given two PDFs, it compares file sizes, designates the larger as the master document, then intelligently replaces pages from the master with matching pages from the smaller file using probabilistic comparison—either by exact page number matching or content similarity analysis. This proved invaluable for construction project paperwork where addendums and revisions arrived as isolated changed pages. Written in C# for performance-critical PDF manipulation and Python for OCR integration, the tool streamlined document management workflows that previously required tedious manual page replacement and verification.
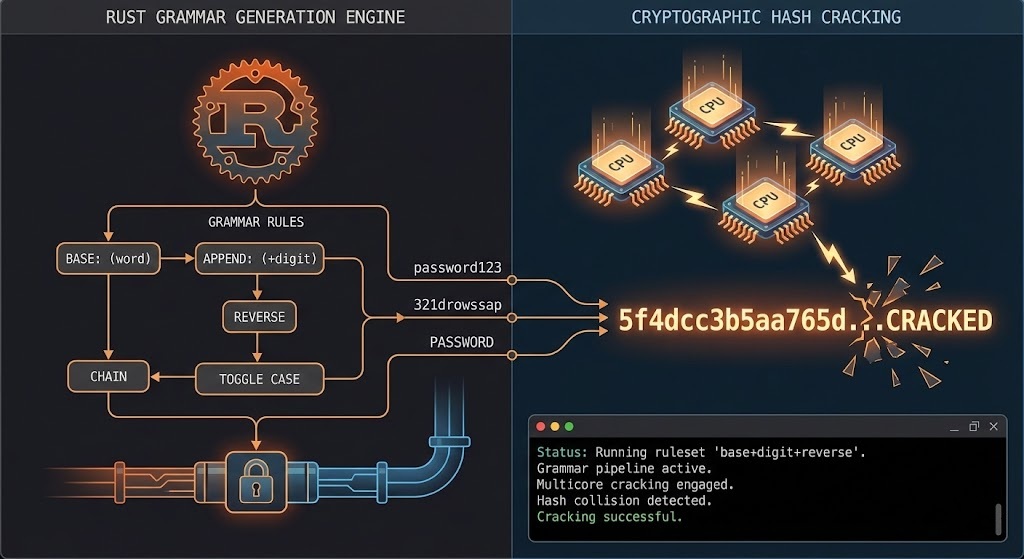
Probabilistic Password Cracking System
Rust-based password generation engine for GPU-accelerated hash cracking.
Probabilistic Password Cracking System
Rust-based password generation engine for GPU-accelerated hash cracking.
This generator uses complex grammatical rules based on the analysis of millions of real world passwords
The generator uses bigram/trigram frequency analysis to produce linguistically valid password bases rather than random strings. The Rust architecture coordinates worker threads via lock-free crossbeam channels, each generating candidates based on learned probability distributions and validating them through 30 fail-fast rules ordered by computational cost—rejecting 92-94% of candidates in the first 8-12 checks. Validated entries pipe directly to hashcat via stdout, where GPU-accelerated hashcat rules apply transformations (capitalization, digit/symbol appends, substitutions) expanding each base into hundreds of variations. This hybrid approach separates intelligent candidate selection (CPU) from brute-force rule application (GPU), maximizing the efficiency of both components.
The attack strategy uses two phases: Phase 1 targets 4-6 character bases with simple hashcat transformations for fast coverage, while Phase 2 focuses on 5-8 character high-probability candidates with complex rule combinations for quality over quantity. Validation rules encode real-world patterns discovered through data analysis: 25.69% of passwords have doubled digits, 4.34% capitalize the first letter, and symbols cluster at specific positions. The hybrid method leverages CPU for probabilistic filtering and GPU for exhaustive rule transformations, ensuring only statistically likely candidates consume computational resources. This probabilistic approach exploits the fundamental weakness in human password creation—people follow predictable patterns that can be mathematically modeled and targeted, making it orders of magnitude more efficient than brute-force enumeration of the entire keyspace.